Pfsense – Connect to VPN PIA
Contents
- 1 Pfsense – Connect to VPN PIA
- 1.1 Setup a PIA VPN with pfSense 2.4.5
- 1.2 Guide
- 1.3 Final Words
- 1.4 Sign up for more like this.
- 1.5 The Best Smart Home Prime Day Deals 2023!
- 1.6 Everything New In Home Assistant 2023.5!
- 1.7 The King Of Video Doorbells – Reolink Video Doorbell Review
- 1.8 Pfsense – Connect to VPN PIA
- 1.9 The plan
- 1.10 Informations
- 1.11 Import certificate authority
- 1.12 Choose the server you want
- 1.13 Connect to VPN
- 1.14 Access the VPN
- 1.15 Route to VPN from default gateway
- 1.16 Rules, to route through VPN
- 1.17 Results
- 1.18 Bonus
Make sure to subscribe below to get notified instantly of the next topic, and as always be sure to let me know if you have any requests for topics.
Setup a PIA VPN with pfSense 2.4.5
Many of us use a VPN in one way or another these days, they have seen a surge in popularity over the last decade or so with many people seeking to use them as means of bypassing content restrictions with Netflix or other streaming services, as a way of connecting to home or work to access documents on the go, or to just retain as much of our privacy online as we can.
As part of the recent pandemic measures here in the UK, I was recently tasked with designing a solution for our enterprise to scale our current VPN solution, which would see around 100-150 users daily, to be able to handle 1000+ users simultaneously in just a few hours. Almost 3 months later, that solution still performs exceptionally well every day. But we are getting a bit of topic here..
Having been a pfSense user for close to 8 years now and a Private Internet Access (PIA) user for coming up to 4 years, I decided it makes sense to document how to setup a PIA VPN with pfSense as a permanent VPN connection, then we will cover how to route certain devices through PIA whilst leaving all other traffic untouched.
This guide uses pfSense 2.4.5-release which is the current version as of the time of writing. Everything is applicable to most older versions although your interface might look a little different depending on your version.
Guide
There is a few different settings you can use with regards to security, what is deemed as “weak” “recommended/medium” and “strong” – I’m going to give recommendations for medium and strong profiles since I see these as acceptable. If performance isn’t quite up to what you were expecting, you can try using the weak profile but I’d recommend going with the medium settings if possible. With that in mind, the recommended and strong settings vary a little in their port selection and certificates:
- Recommended: UDP Port 1198 with AES-128 for encryption
- Strong: UDP Port 1197 with AES-256 for encryption
To give you some reference, the APU2 that I reviewed here is capable of 100mbps over VPN using the recommended security we see here, but cannot get close to the 300mbps my link is capable of. Perhaps time to upgrade..
Certificate installation
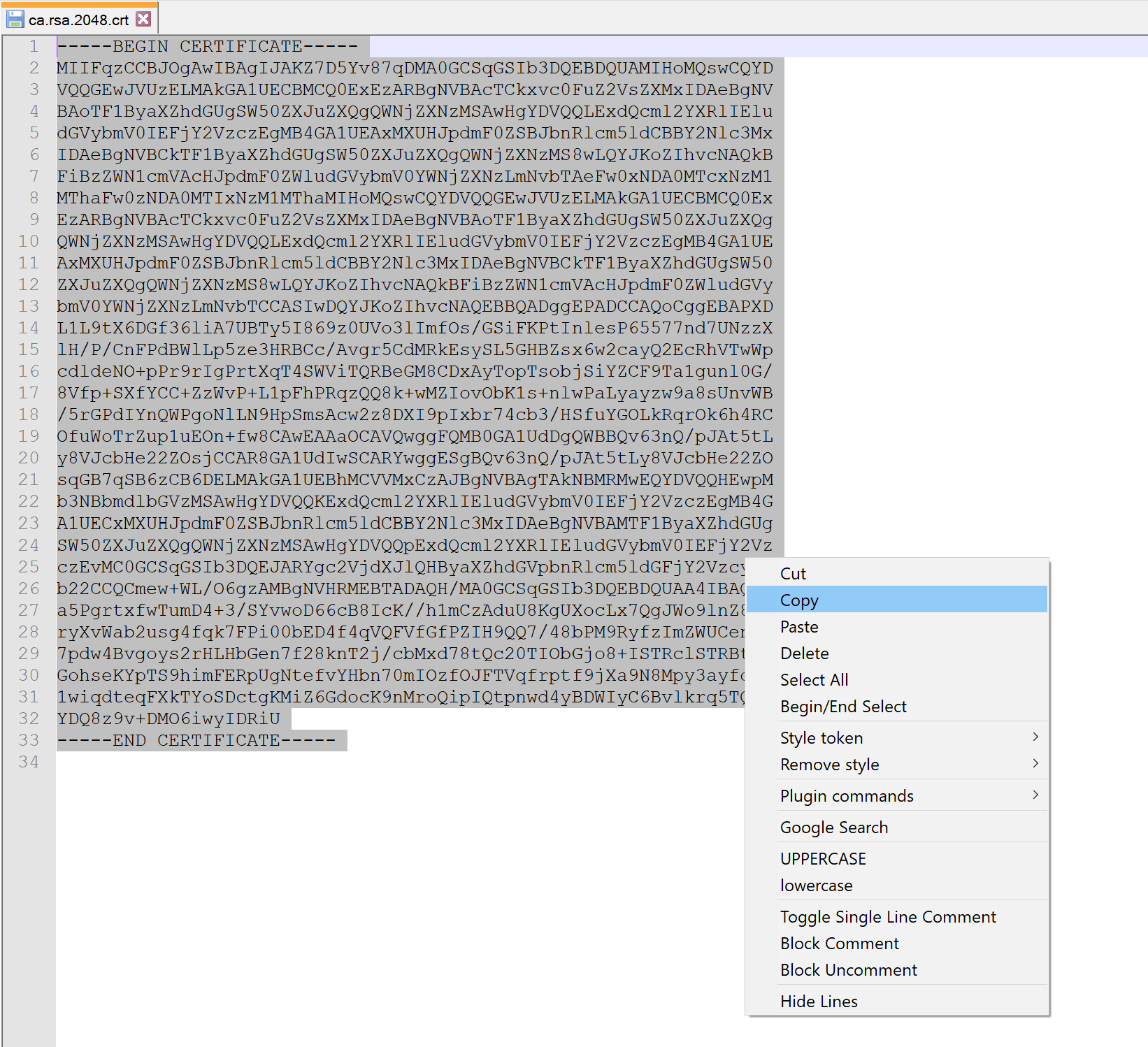
First we need to install the PIA CA certificates into pfSense so that we can use them within the VPN configuration.
First download the correct certificate here:
Once downloaded, open the file in notepad/notepad++ and highlight everything within the file and copy to clipboard:
Next, head to System > Certificate Manager and make sure you are on the CAs tab. Click Add to create a new Certificate Authority. Give a descriptive name and change the method to “Import an existing Certificate Authority“. Then in the Certificate data box, paste the certificate data you copied:
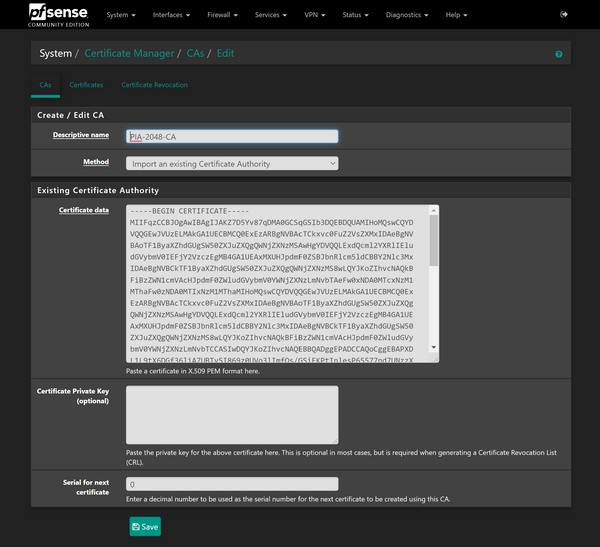
Finally hit Save to create that CA. If everything worked, you will now have a new CA listed in the table and the “Distinguished name” (DN) column will have pre-populated information:

OpenVPN Setup
We need to decide which server location we want to connect to, PIA currently has 3300 servers in 68 locations across 47 countries, so quite a wide range.
Head to this link here.
Then select the server you want to use, you can repeat this for as many servers as you want to use, you might want one in the UK and one in the US. Select a location, then copy the address you want to use. For example, clicking on the UK reveals 3 VPN servers, select the address of the one you want to use, I am using the London one in this example:
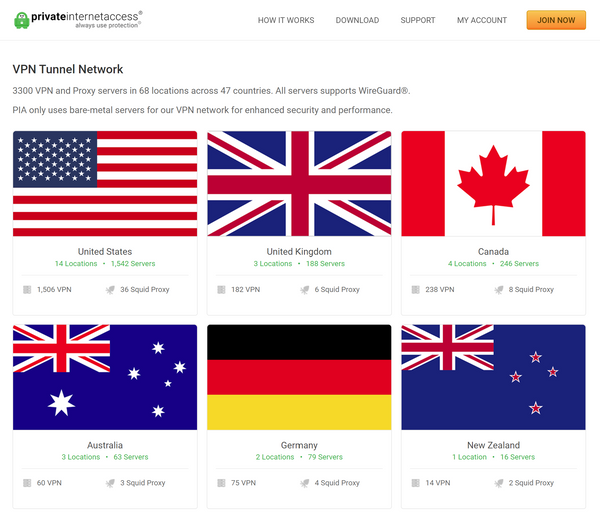
Copy this address. I am using uk-london.privateinternetaccess.com for this example.
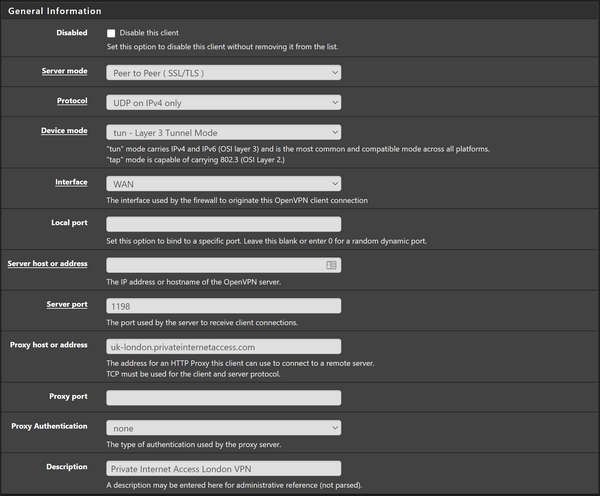
Head over to VPN > Clients > Add to add a new VPN client.
Many of the settings can be left at default, if I do not mention them then they are the stock settings so refer to the images for what they should be.
General Information
In the General Information section change the following values:
- Server host or address: uk-london.privateinternetaccess.com (or whichever location you copied above.
- Server port: 1198 or 1197 depending on which security level you want.
- Description: Private Internet Access London VPN
You should have something looking like this:
User Authentication
In the user authentication settings section, enter your PIA username and password. You can find your username in your account on the PIA website, it usually starts with the letter “p” followed by numbers.
I would personally leave Authentication Retry unchecked which will automatically re-connect if the connection is dropped. If you have issues with this you can tick the box to disable it.
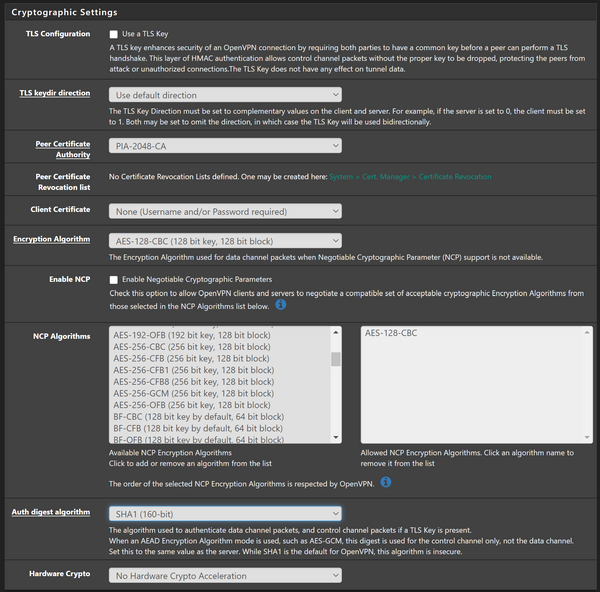
Cryptographic Settings
Under the Cryptographic Settings section make sure to change the following settings:
- TLS Configuration – Uncheck
- Peer Certificate Authority –PIA-2048-CA (the descriptive name you gave the CA earlier)
- Encryption Algorithm –AES-128-CBC
- Enable NCP – Uncheck
- Auth digest algorithm – SHA1 (160-bit) for medium security, SHA256 (256-bit) for strong security.
- Hardware Crypto – if you have AES-NI acceleration available, select that from the list, or leave set to “No Hardware Crypto Acceleration” initially and come back and change afterwards to tweak performance.
You should have something that looks like the following:
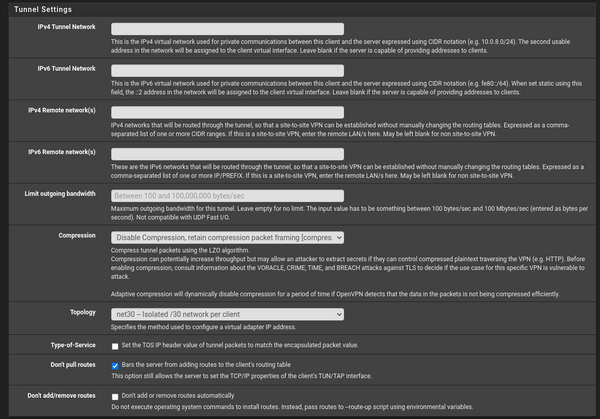
Tunnel Settings
There is just a few settings to change in this section and they are:
- Topology –net30
- Don’t pull routes – If you want all devices on your network to go through the VPN, leave this unchecked. If you want to selectively control which devices go through the VPN and which don’t, check this box.
That’s all we need to change for this particular setup, should look like this:
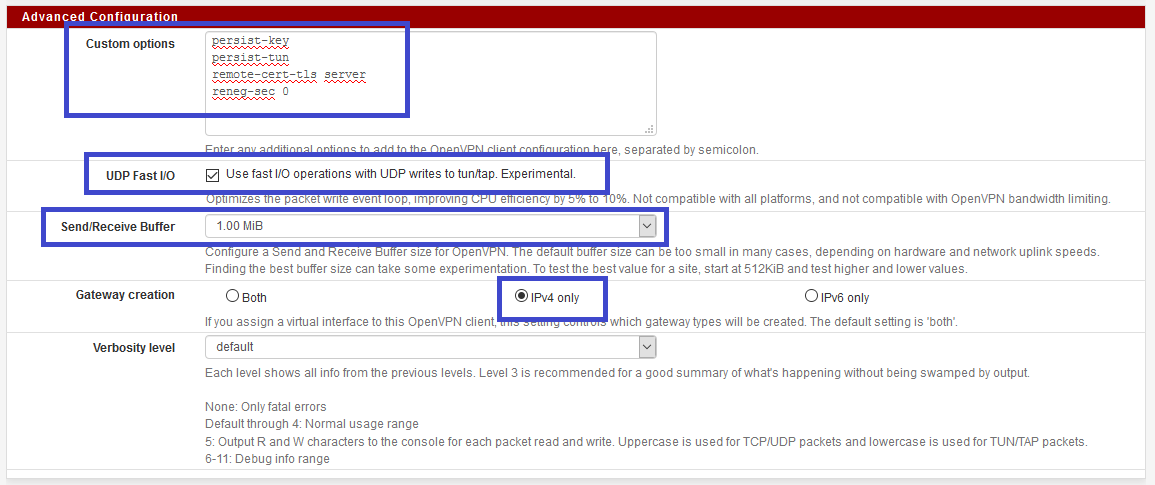
Advanced Configuration
Finally, in the Advanced Configuration, enter the following values:
remote-cert-tls server persist-tun persist-key reneg-sec 0Then set the following:
- UDP Fast I/O –check this to improve performance, you can come back and uncheck it later if you have issues.
- Send/Receive Buffer – You can play around with this setting, but I’ve always found 512 KiB setting to be pretty good. Tweak these settings later to see what gives you better speed.
- Gateway creation – IPv4
With the final settings looking like this:
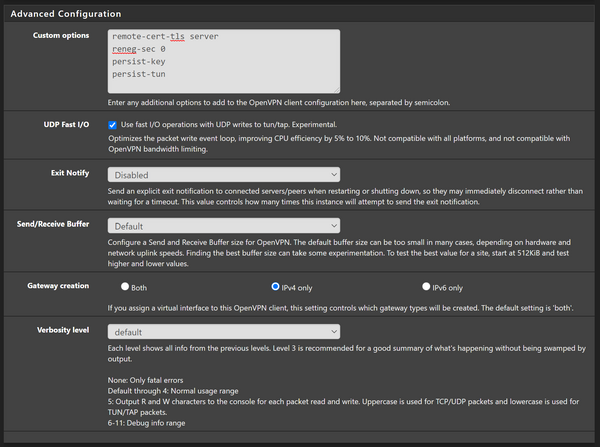
Finally hit Save!
Checking status
We can now check that the VPN connection has been established, head over to Status > OpenVPN and under the Client Instance Statistics section you should see the VPN connection we just made. Look in the status box and confirm the status is “Up”:
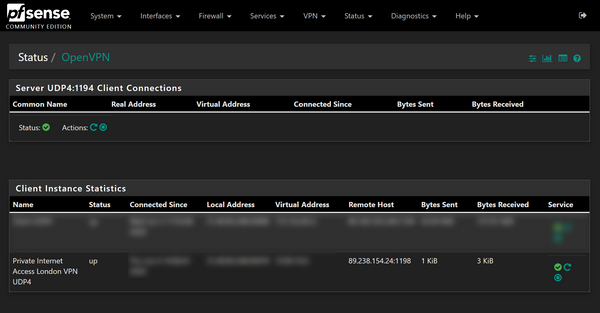
So head over to Google and type “What is my IP” and you will see your IP address has changed to the PIA address right? Wrong.
We haven’t changed any of the routing within pfSense so it doesn’t yet know to send the traffic over VPN rather than the WAN. Let’s change that.
Creating Interfaces
Its not required but I prefer to create an interface for the newly created VPN.
Go to Interfaces > Assignments. From there you will have a list of all the interface assignments you have on your system, don’t worry if you don’t have as many as me, you probably just have WAN and LAN. In the Available Network Ports drop down, select the PIA VPN option from the list, then press add:
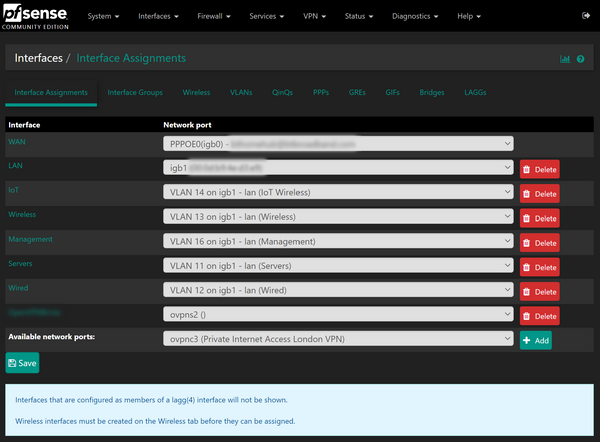
A new interface will have been created called OPTX, go ahead and click on this to edit it. From the edit page, check the enable box and change the description to something more suitable. Hit Save then press apply changes:
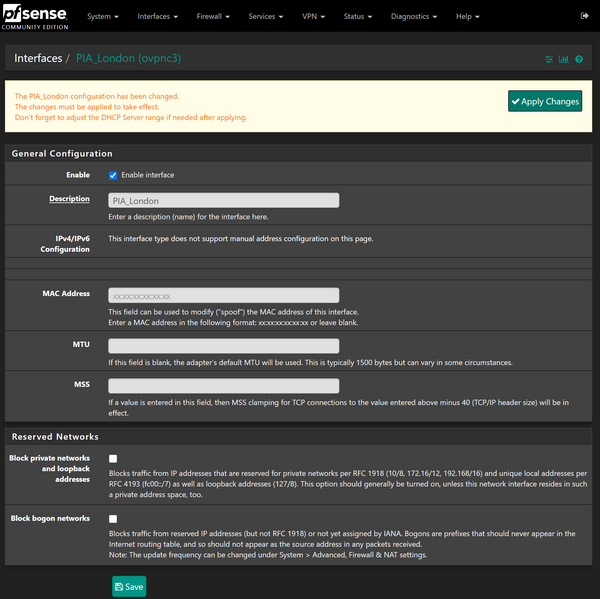
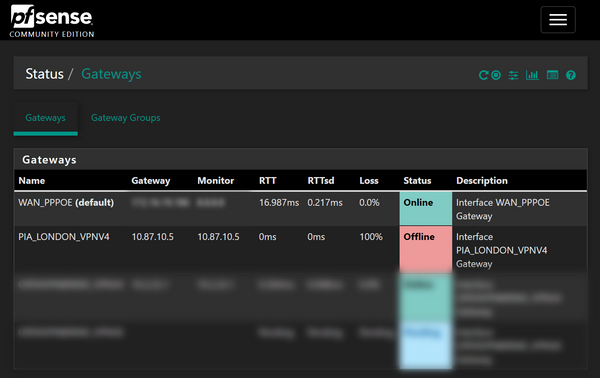
From here, go to Status > Gateways. Notice how it says Gateway down for the PIA gateway? We don’t need to correct this per say, but we should to save things flagging up as down in the logs:
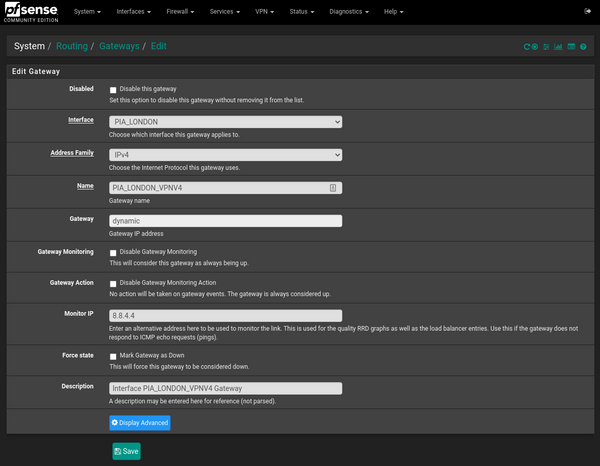
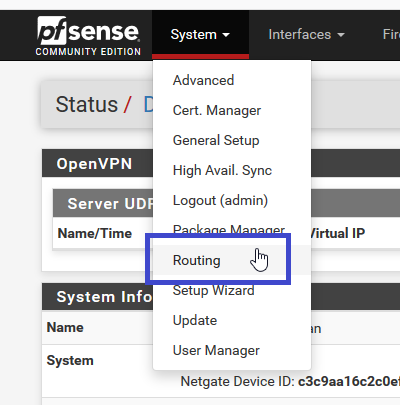
Go to System > Routing and edit the automatically created PIA gateway. In the Monitor IP, enter an IP to use as an alternative, I’m using 8.8.4.4 here:
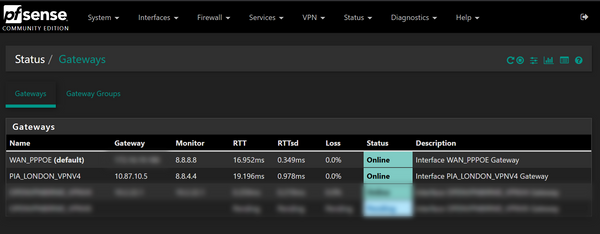
Now head back to Status > Gateways and confirm the PIA gateway is online:
Creating Aliases
An alias allows us to define groups of IP’s or networks together so that we can use one alias to quickly reference all networks we want to use instead of typing them out everytime.
Head to Firewall > Aliases and press add. Note at the top you have different types of Aliases – IP, Ports and URLs. We are just using the IP aliases for now.
Name this PIA_Traffic, give it a description and choose Networks as the type. Enter all the subnets/networks you want to go via PIA. You can enter individual IP addresses by using the /32 mask, which I will show you now:
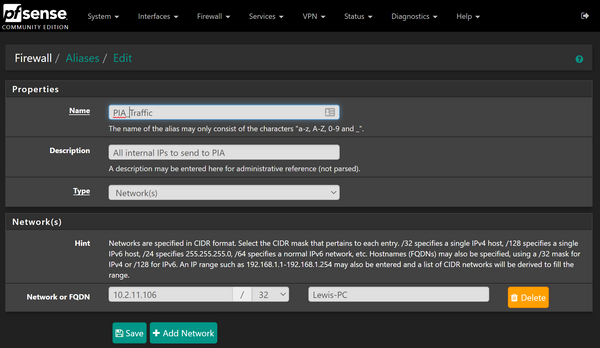
You can add as many as you want, I’m just adding one for this example, which does kind of defeat the purpose but I’d still advise it as it allows you to quickly add more in the future.
Hit save and then apply changes.
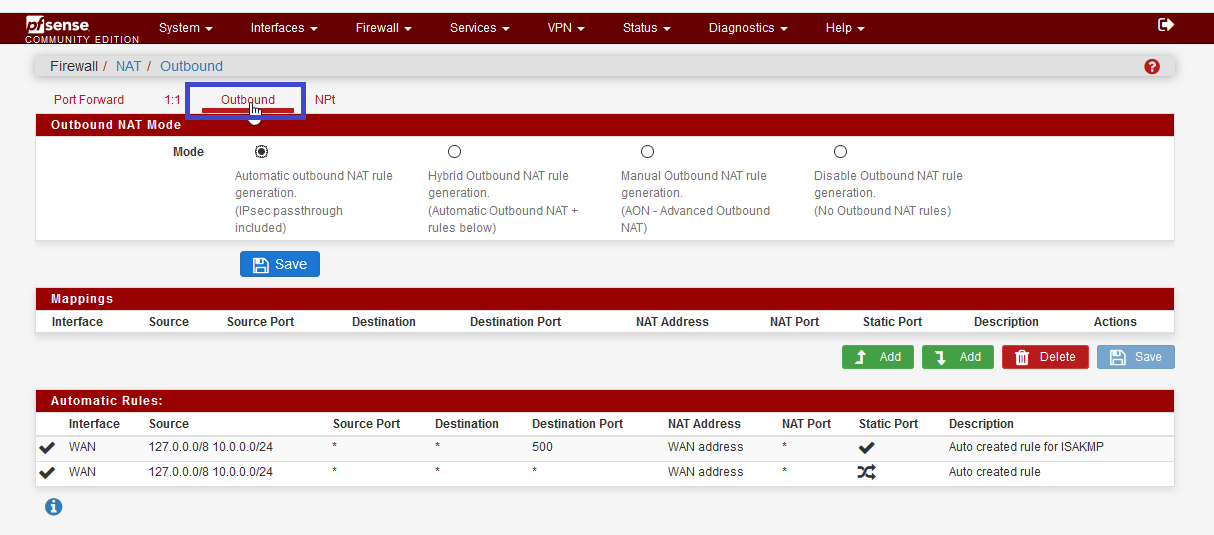
Outbound NATs
Network Address Translation or NAT is the process of remapping an IP address as the packets are in transit. The most common type of this probably happens without you realising – when you access the internet from your computer/laptop/phone all of these devices are exposed as one single public IP address.
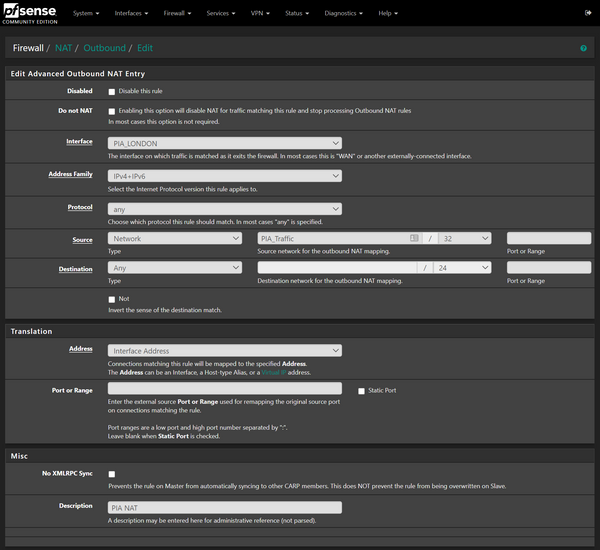
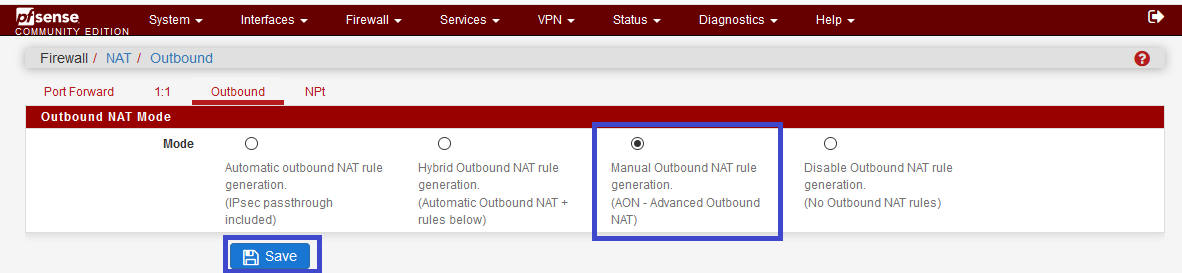
Anyways, we need to create an Outbound NAT in order to send traffic via the PIA VPN. Go to Firewall > NAT > Outbound and change the Outbound NAT mode from Automatic to Hybrid. You can use manual if you wish, but I prefer Hybrid for speed.
You will notice you now have a mappings section (which is blank) and an Automatic rules section which will have all the automatically generated rules for the WAN addresses. Go ahead and click add to add a new mapping.
Set the following:
- Interface –ensure to select the PIA interface we created earlier.
- Address Family – IPv4+IPv6
- Protocol– Any
- Source – Choose Network as the type, then type PIA into the source network box, and the Alias we created earlier will show up. Click to select it.
- Destination –any
- Description – PIA NAT
The rule will look like so:
Then create another with the same settings except this time we set a destination port like this:

Note how the static port box is checked also.
Make sure the rules look like this on the Outbound NAT page:
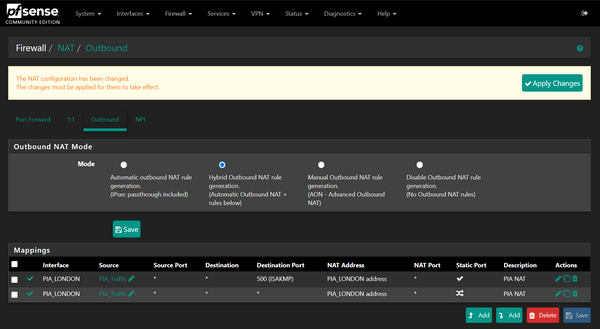
Go ahead and press apply changes.
Firewall Rules
We are almost there! This is the last step. Go to Firewall > Rules and select the interface(s) that your network resides on (probably LAN if you are unsure). We need to create 2 rules here, one that allows traffic from the PIA_Traffic aliases to the PIA gateway, and another just below it that denies it to all other traffic. This means if you lose connection to the VPN, traffic won’t start flowing through the regular WAN interface.
Press add and create a rule like so:
Before saving, click Display Advanced and in the Gateway box set the PIA gateway:
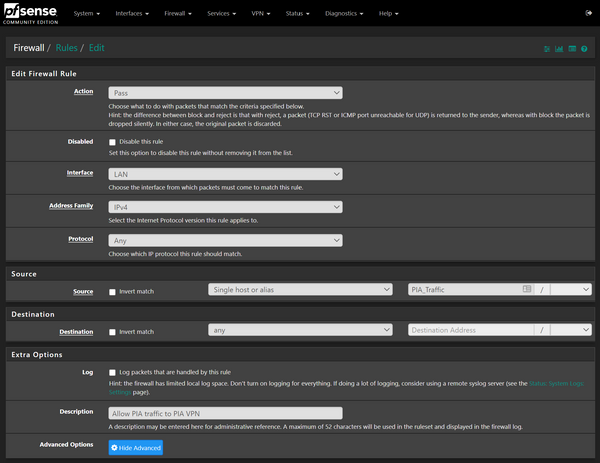
Press save, then create a second rule like this:
No need to set the gateway this time:

Press save. Make sure the rules are configured like so, I am using pfBlockerNG so I have an extra block rule (the second one) but otherwise the PIA Accept rule should be the first of those 2, PIA block rule directly below that, followed by the other rules. Should look something like this:
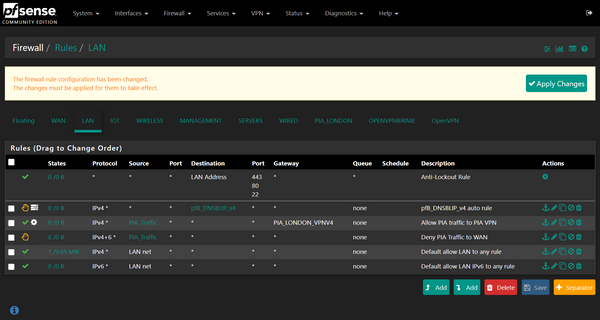
Make sure to hit apply changes once you are happy.
And that’s everything you’ll be glad to know!
Testing
Go ahead and give it a test out by going to Google and typing what is my IP – it should be one of the PIA ones and not your normal one.
I’d also recommend running a speed test and making sure you are getting the correct speeds you would normally expect. Then you can tweak with some of the VPN settings if required.
Further Steps
A few things to consider are ensuring that you are using the PIA DNS servers if you are routing all traffic via the VPN, or if you are doing it on a per device basis consider setting the DNS servers to the PIA ones on these devices. Ensure you are using DNS over TLS to make sure you are getting DNS leak protection.
Additionally you may want to repeat the steps above to create different VPNs so you can have access to different countries if you so require it.
Final Words
I hope you managed to get everything working create a PIA VPN with pfSense, whether it be for getting additional shows through Netflix, bypassing ISP restrictions or just increasing your privacy online.
Make sure to subscribe below to get notified instantly of the next topic, and as always be sure to let me know if you have any requests for topics.
Sign up for more like this.
Enter your email

The Best Smart Home Prime Day Deals 2023!
Amazon Prime Day 2023 is here on the 11th and 12th of July 2023! These are all of the best Smart Home Deals I have found for you today!
Lewis Barclay Jul 11, 2023 • 1 min read

Everything New In Home Assistant 2023.5!
Upgrade your smart home game with Home Assistant’s latest voice features! Assistant pipelines, ESPHome smart speakers, VOIP, and more!
Lewis Barclay May 8, 2023 • 4 min read

The King Of Video Doorbells – Reolink Video Doorbell Review
The Reolink Video Doorbell features good image quality, person detection, PoE, motion zones, RTSP, Home Assistant integration and more!
Pfsense – Connect to VPN PIA
This tutorial use : https://www.privateinternetaccess.com as VPN but the operation will be mostly the same with another provider.
I will explain how to connect your PfSense to PIA VPN and chose which device you want to “protect” with.
In this tutorial I’ll use the recommanded ciphering, for a balance use of CPU / security.
The plan
Here’s the setup without VPN, normal PfSense, allow devices from LAN and DMZ to go on WAN.
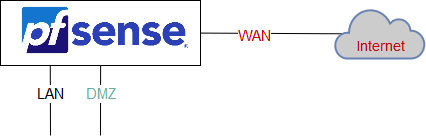
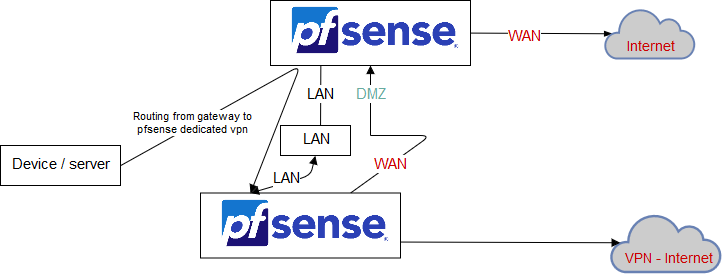
We want : a second PfSense, dedicated to permanent VPN connexion.
The PfSense at the top is the default gateway of all device / server, nammed pfsense.pla01.lbdg.lan. We’re gonna use him to route some servers / devices into the VPN.
The PfSense at the bottom will be the VPN, he use the DMZ interface, to have an internet connexion.
Informations
| Hostname | LAN IP address | Theme | Description |
|---|---|---|---|
| pfsense.pla01.lbdg.lan | 10.0.0.1 | Normal | default gateway of all my devices (on the top of the scheme) |
| pfsense-vpn-tuto.pla01.lbdg.lan | 10.0.0.5 | Red | pfsense dedicated for the VPN (on the bottom of the scheme) |
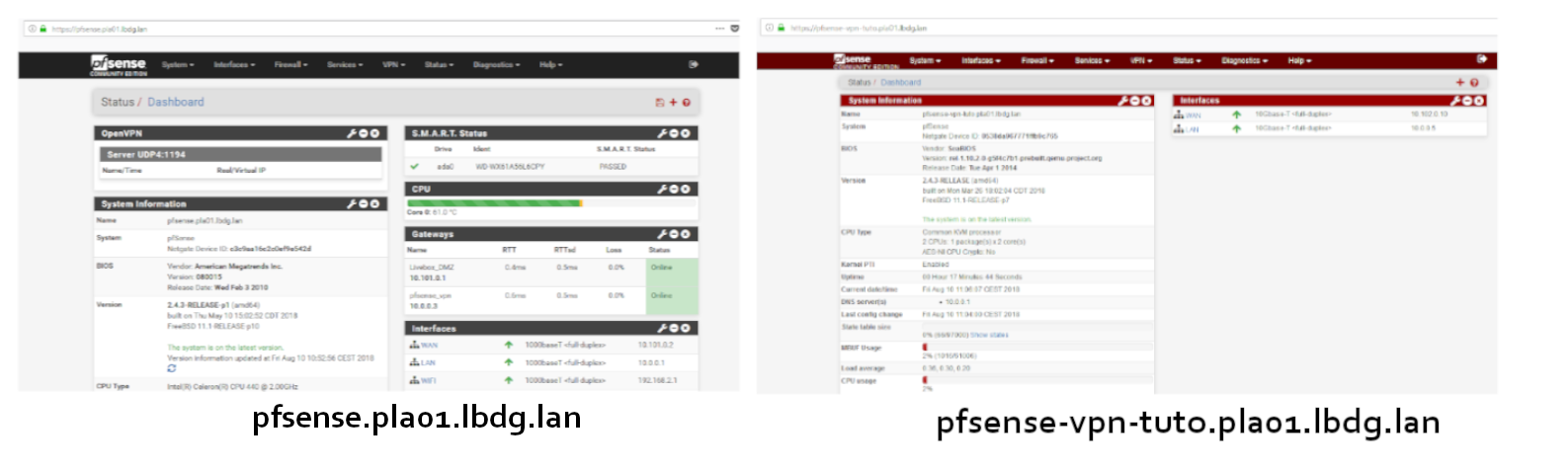
I use different PfSense theme, it helps to see the difference between the two PfSense
First, you should download and import the PIA CA on your PfSense (so, all the certificate from signed from this CA will be accepted).
Here you can find the CA : https://www.privateinternetaccess.com/openvpn/ca.rsa.2048.crt (right click, save the target as)
Now, you need to open the ca.rsa.2048.crt file with a text editor, and copy the content in the clipboard.
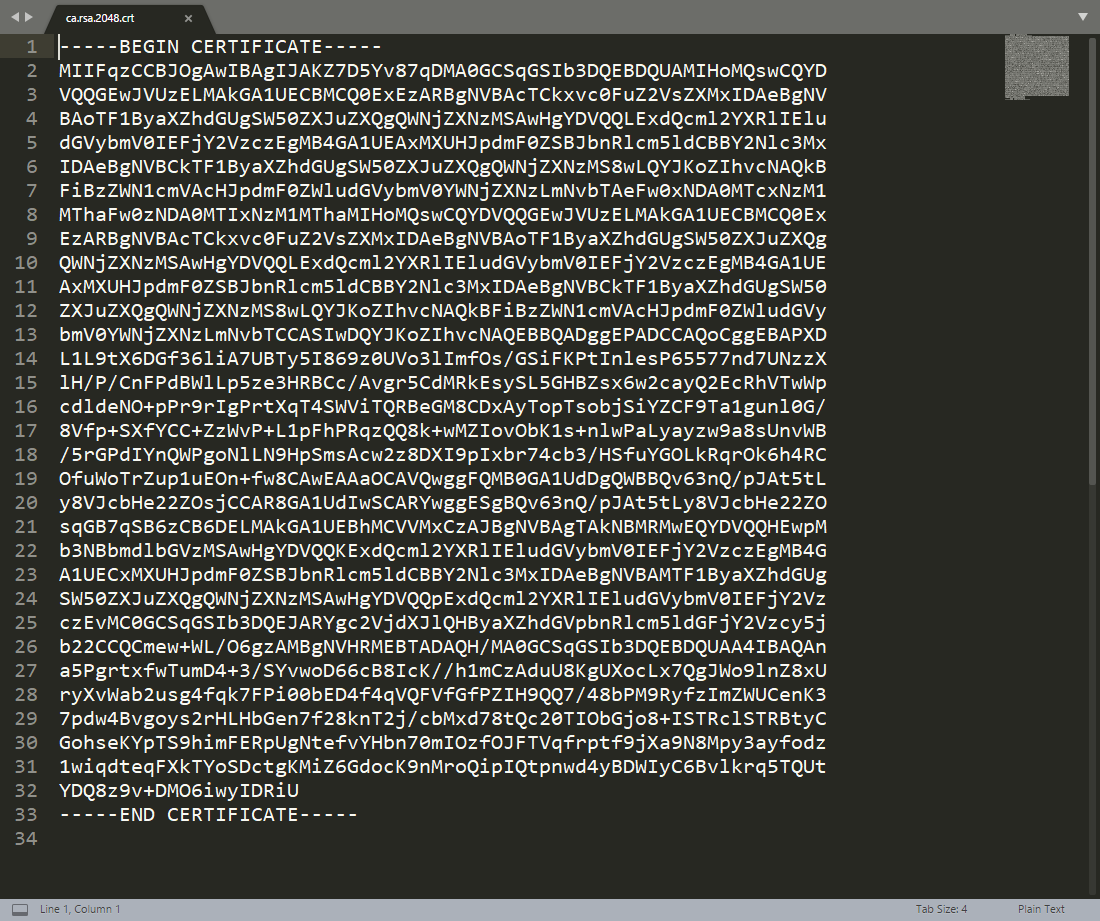
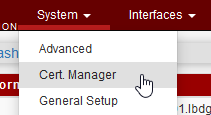
On pfsense-vpn-tuto, go to : System => Cert. manager
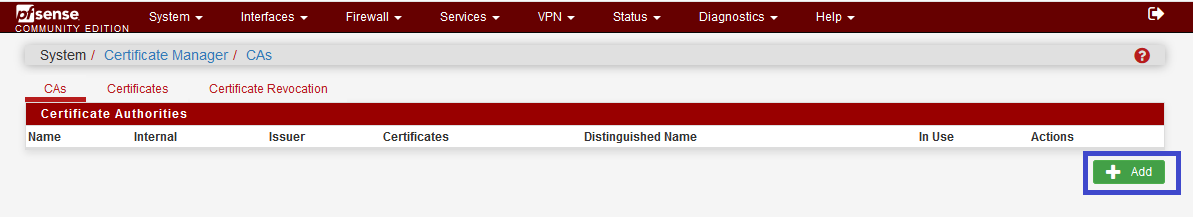
In certificate data, paste CA file content 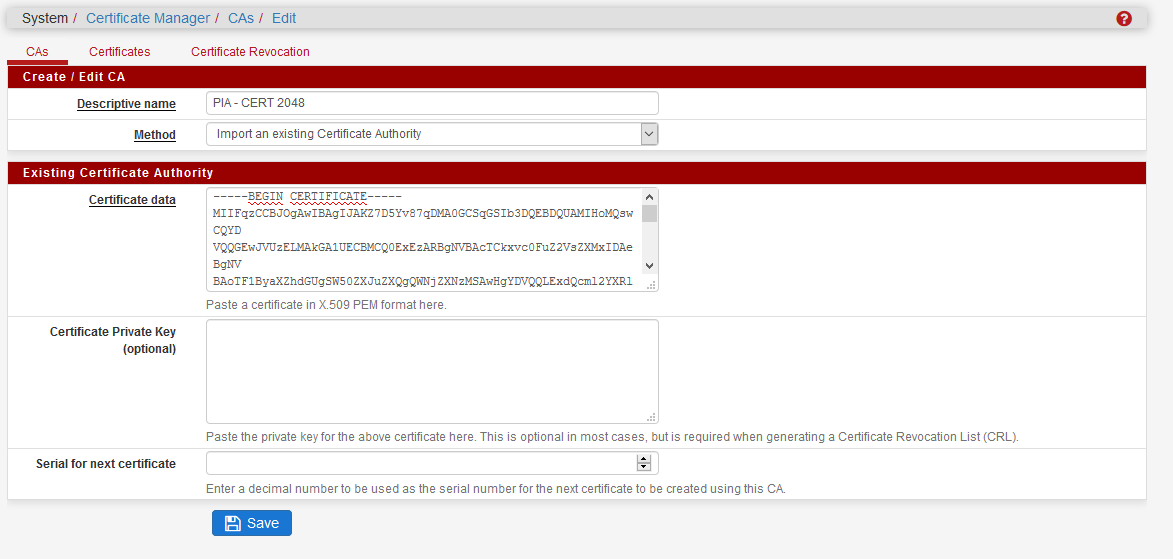
Choose the server you want
PIA give you the choice of lot of server, here’s the page to choose : https://www.privateinternetaccess.com/pages/network/
First, I wanted use a server from US, so I tested it out some :
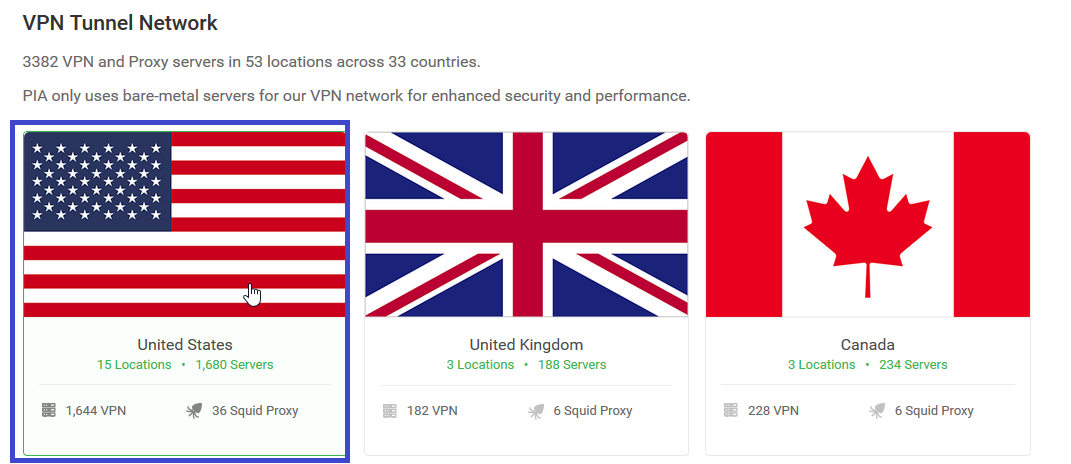
Random server, in California 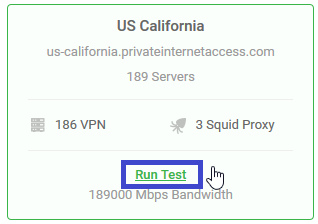
Run the test 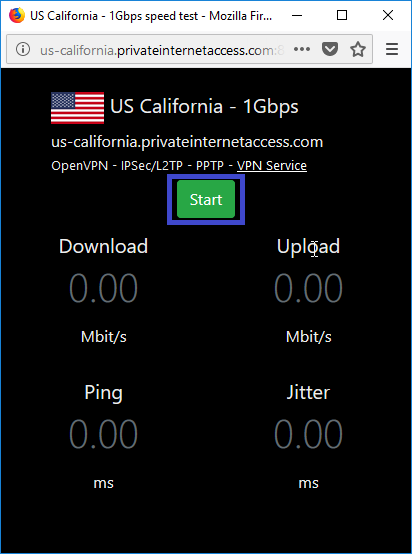
And . The result is pretty bad (ping = awfull) 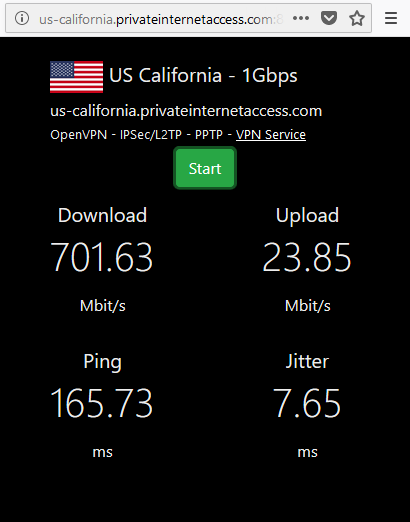
I made some others tests, and finally find the good one :
The VPN server is : uk-london.privateinternetaccess.com (remember this)
Connect to VPN
In the VPN configuration, scroll to OpenVPN => Client, add a new client 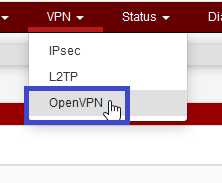
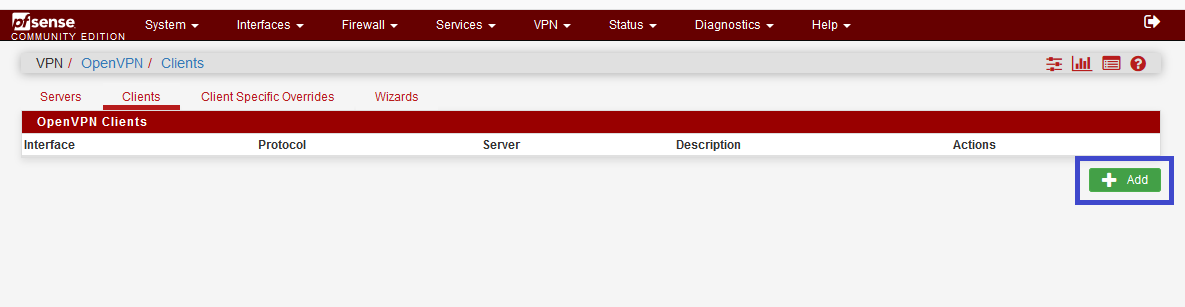
You need to fill :
- the hostname server retrieved from the tests (uk-london.privateinternetaccess.com)
- the port 1198
- your username and password from PIA
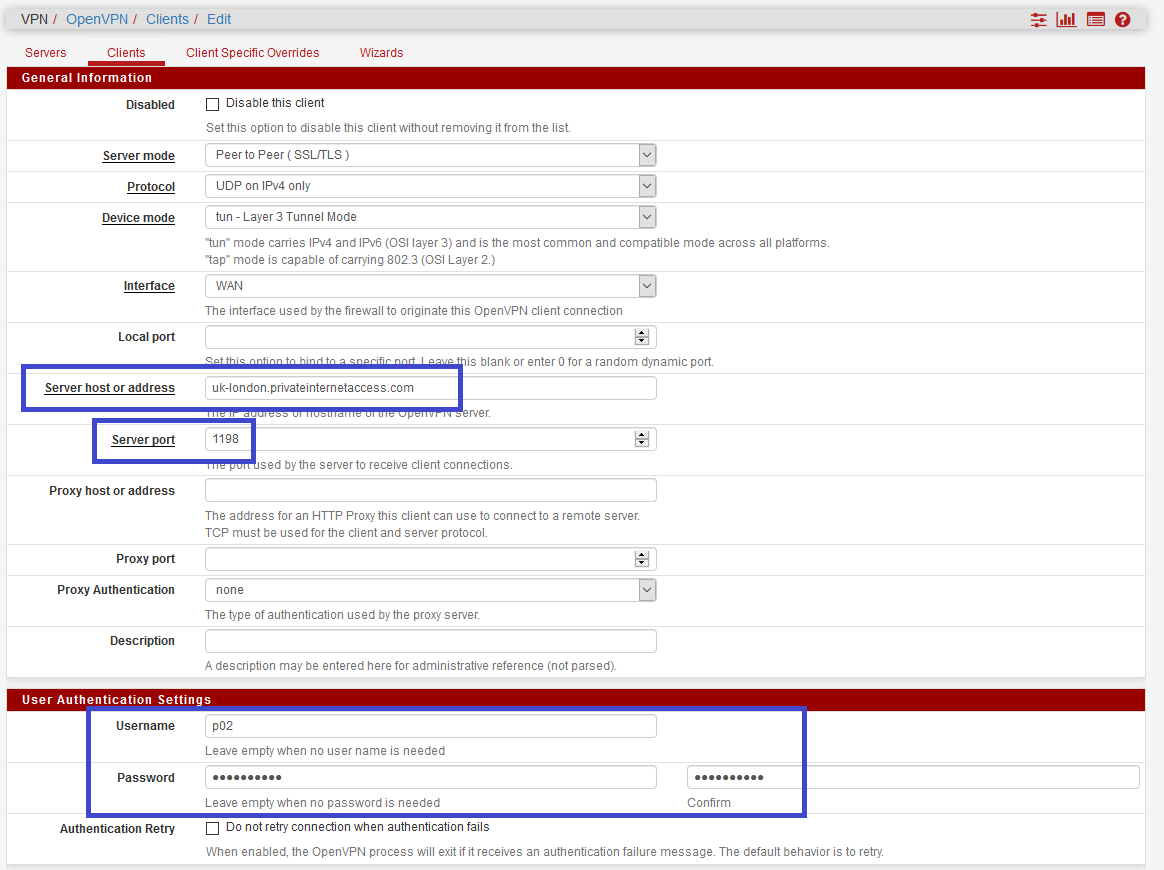
PIA don’t use TLS key, so, uncheck it.
They’ll use AES-128-CBC (which is pretty good) and NCP with algo : AES-128-CBC & AES-256-CBC. Auth digest should be sha1.
For hardware crypto, it will depend on your hardware, but use BSD cryptodev engine if can 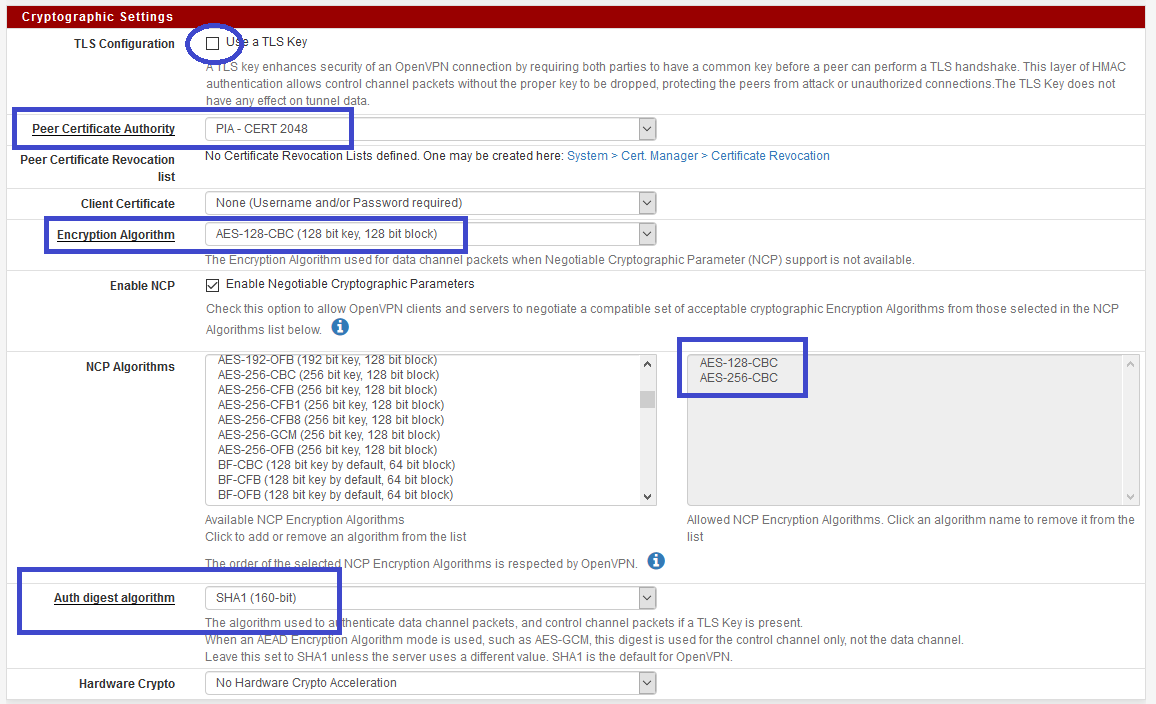
Leave Tunnel Settings by default
In the adanced configuration
Add following parameters to the custom options :
persist-key persist-tun remote-cert-tls server reneg-sec 0 Use fast I/O AND change buffer size, the perfect balance for me, is 1 MB.
And, hit save button. 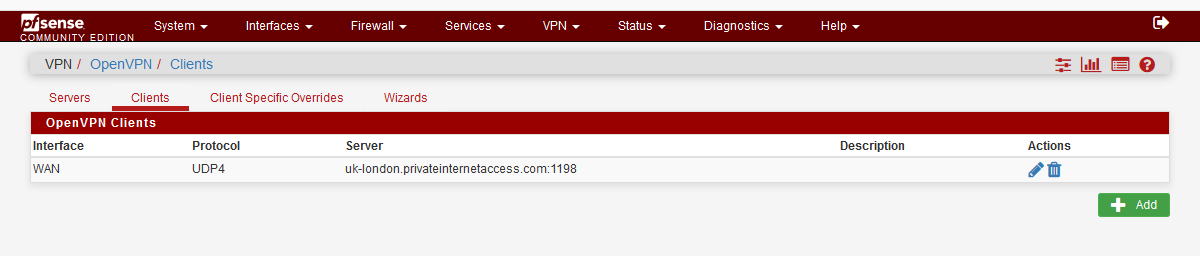
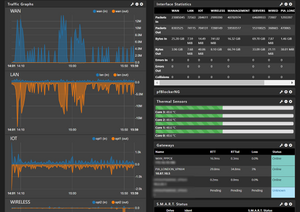
Now, we need to check if the VPN is mounted. Click on status, scroll to OpenVPN :
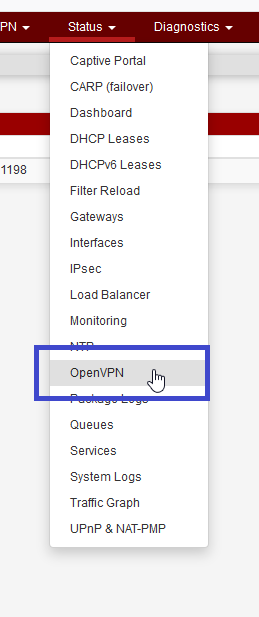
If the status stay down it migh be a configuration problem / port opening through WAN.
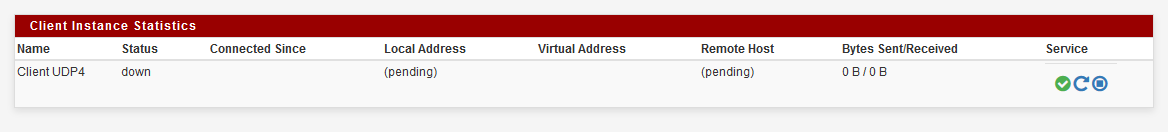
Otherwise 
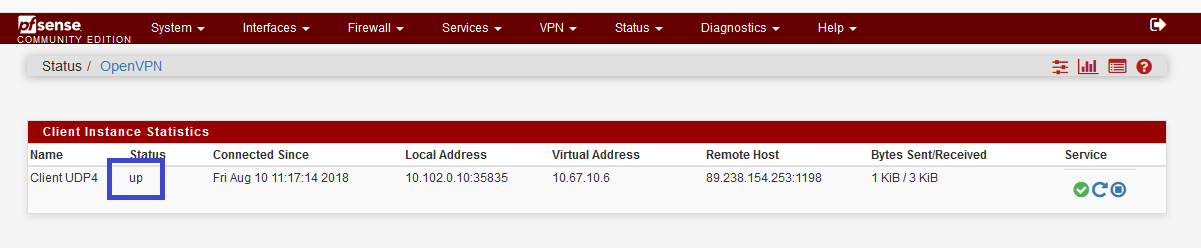
The VPN is now up and running !
Access the VPN
We are now connected to a new “gateway”. So we need to configure NAT, to permit device to NAT on this “gateway”.
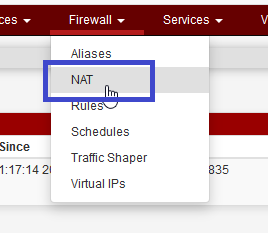
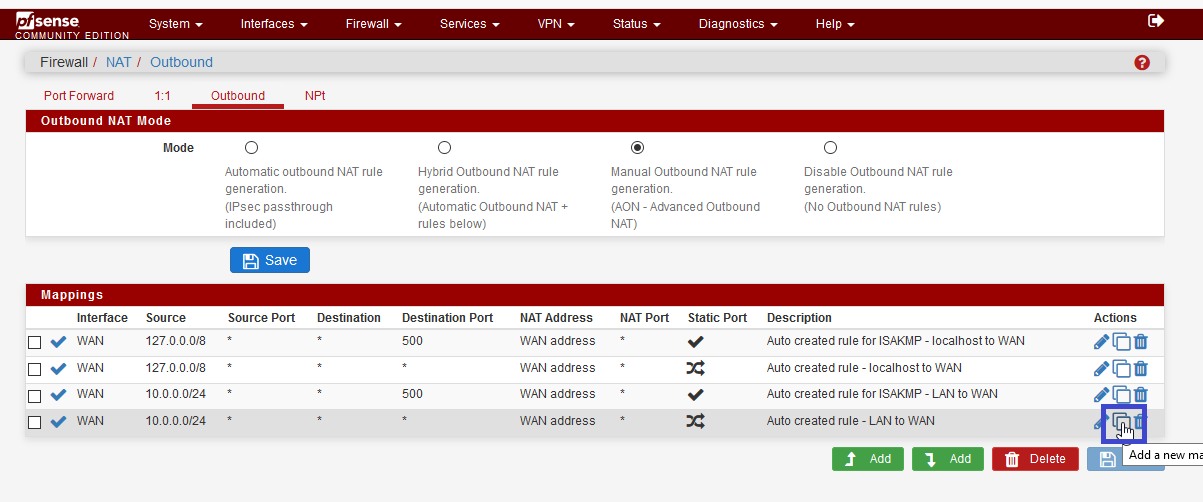
Change WAN interface, by OpenVPN interface, and change the description. 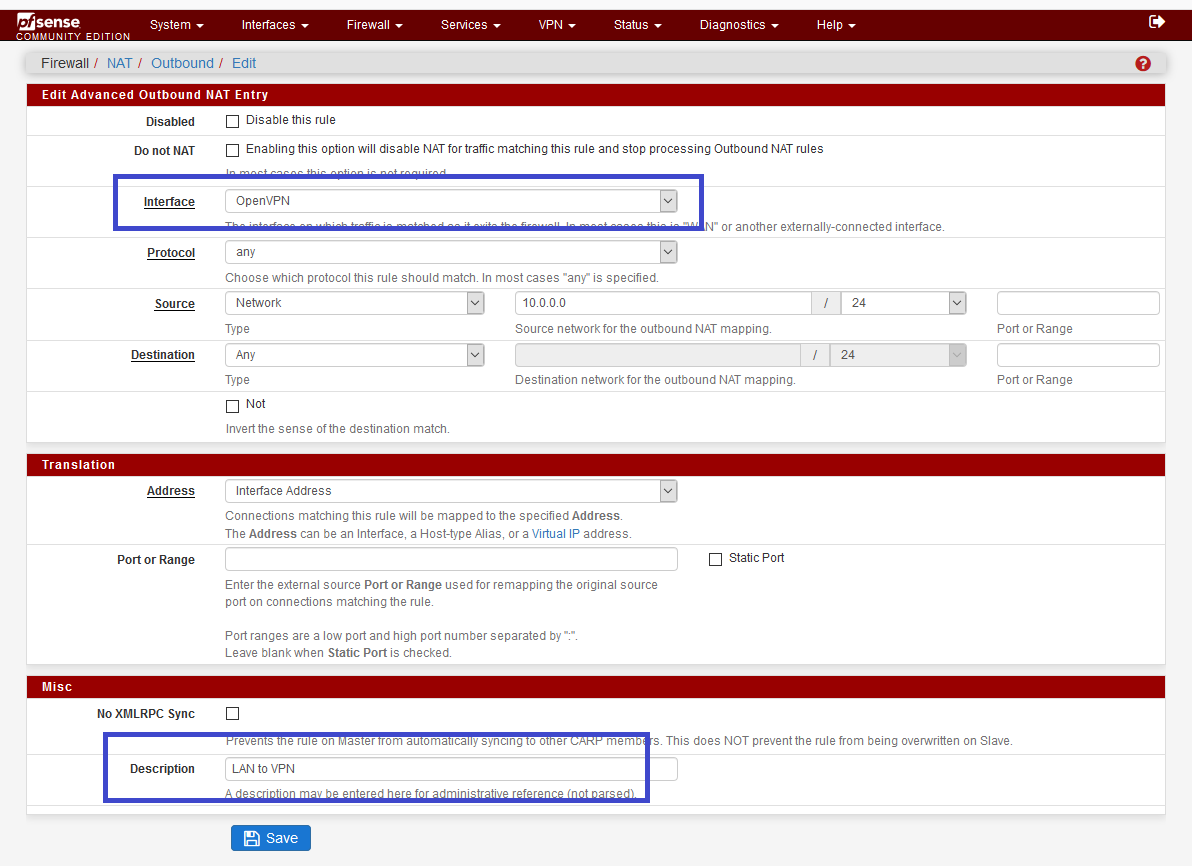
Now, our devices could NAT on OpenVPN “gateway”.
Route to VPN from default gateway
Now, we have to work on our default gateway, which is pfsense.pla01.lbdg.lan. We have to declare the new gateway pfsense-vpn-tuto (10.0.0.5) for the LAN.
Livebox_DMZ is my internet connexion (ISP doesn’t provide a bridge mode) 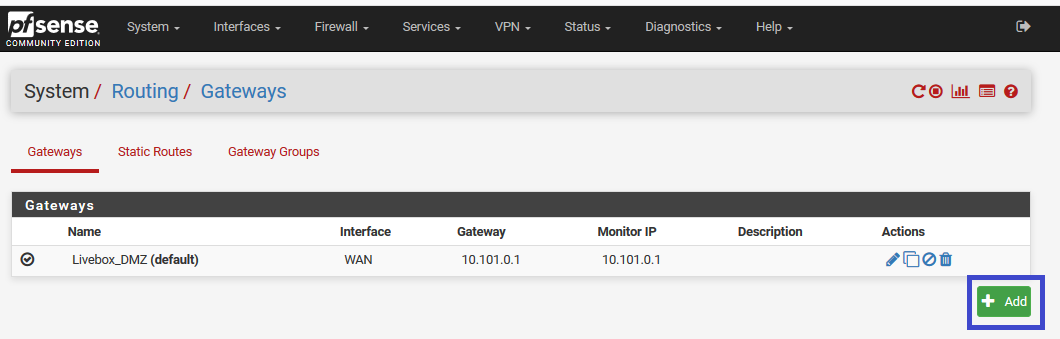
Create the gateway on the LAN 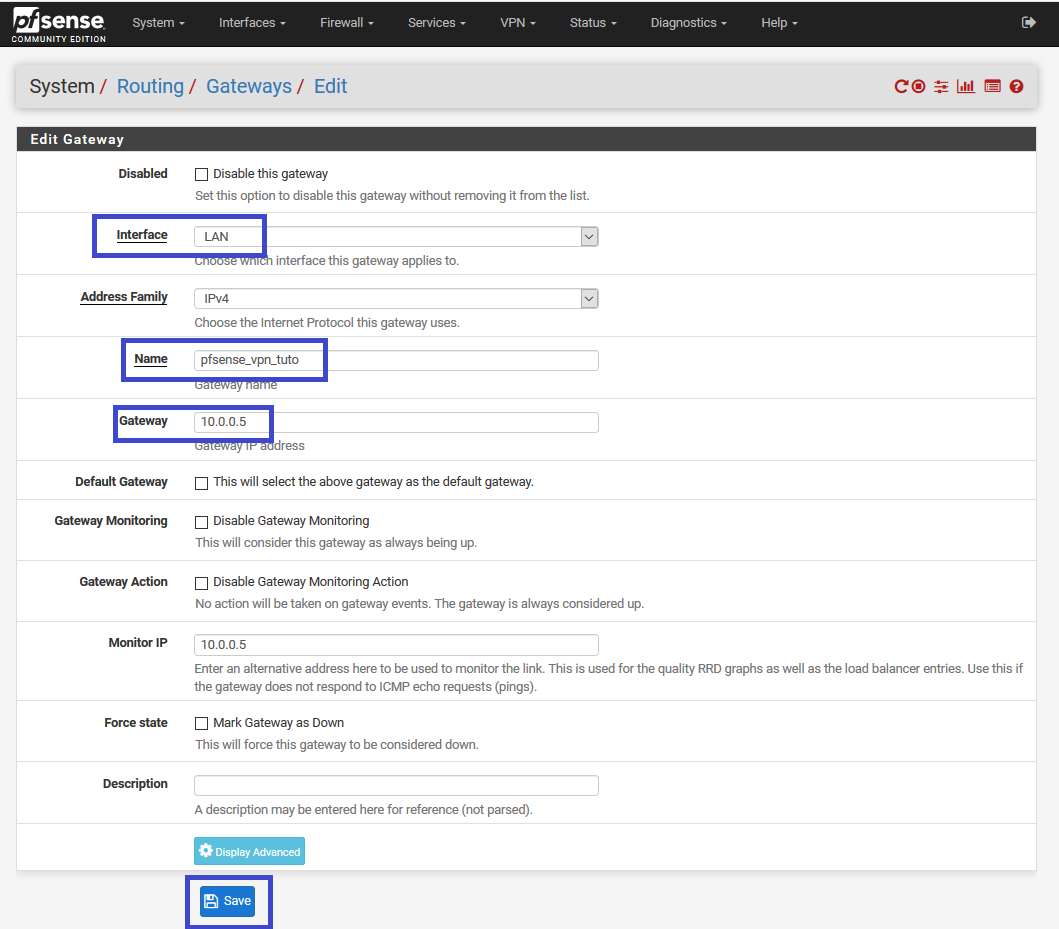
Now, we could use this gateway on rules, what we’re gonna do. 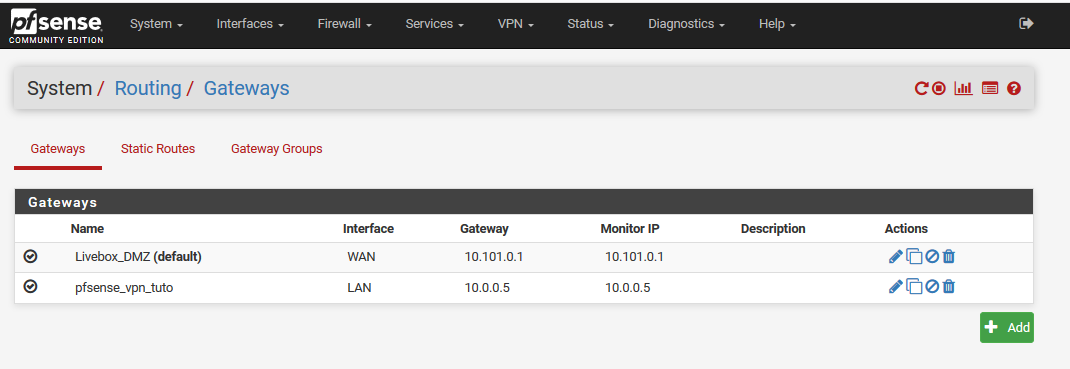
Rules, to route through VPN
Because we want to choose which device will pass through the VPN, we’re gonna create specific rules for that : 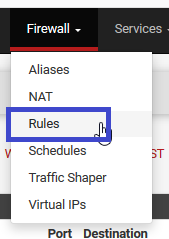
Create a new simple rule, IPv4, all protocol (will depend on what you want), as source, the device you want to pass through VPN (10.0.0.52 is my laptot), and destination (any) 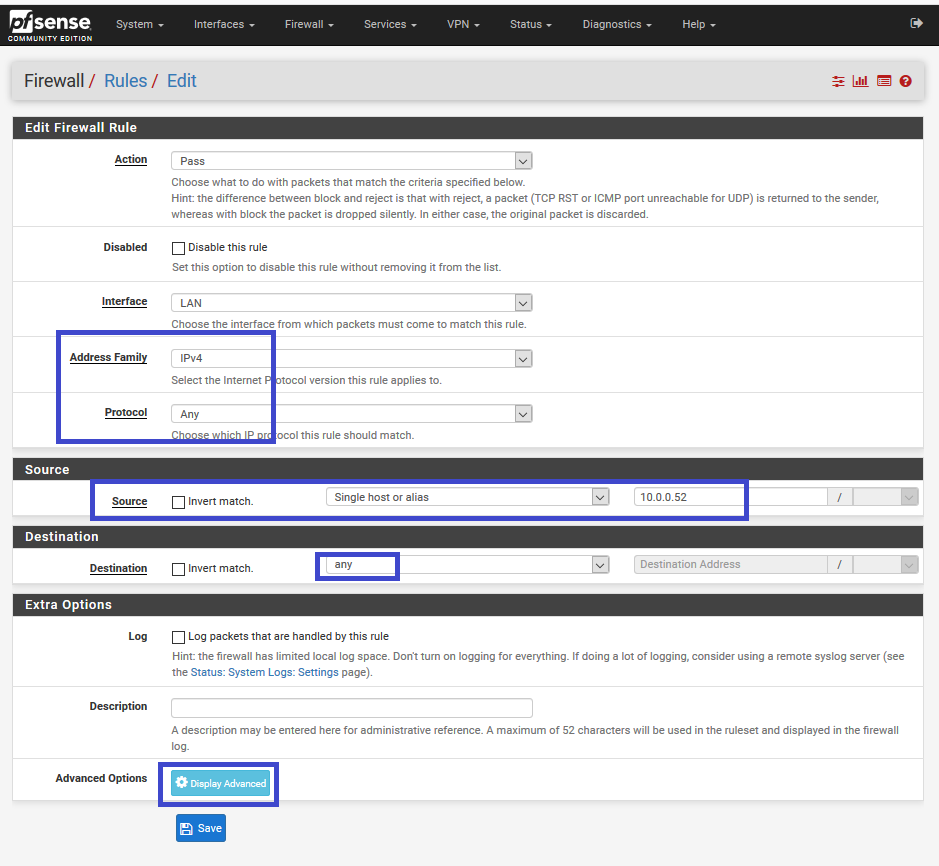
On the advanced option, search for state type and select none 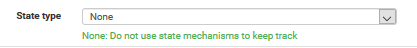
Lower, change the gateway to pfsense_vpn_tuto 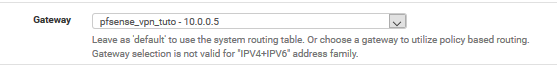
Final rule : 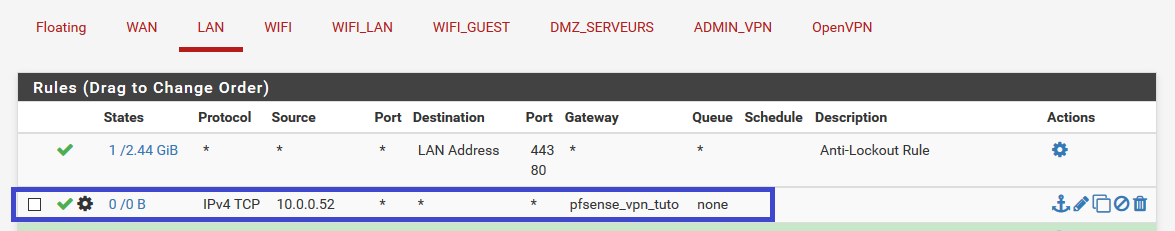
Now, if the rule matchs, connexion will be routed to 10.0.0.5 and NATed to VPN
Results
My previous IP address on internet 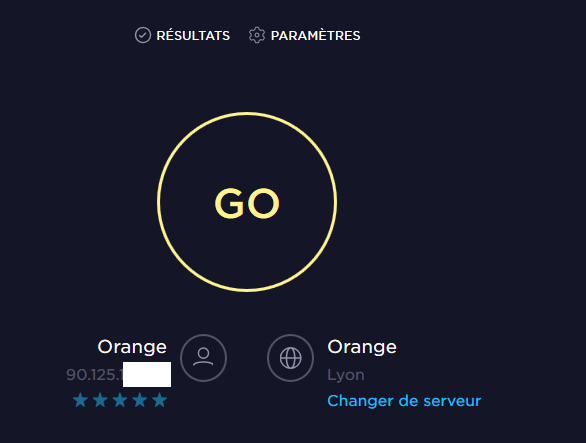
Now, with the VPN and the rules : 
Thanks for reading, if you have any question, feel free to react on this reddit thread : Reddit thread
Bonus
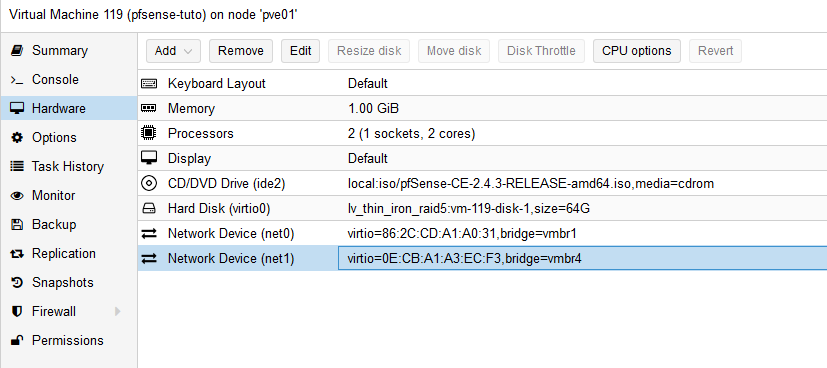
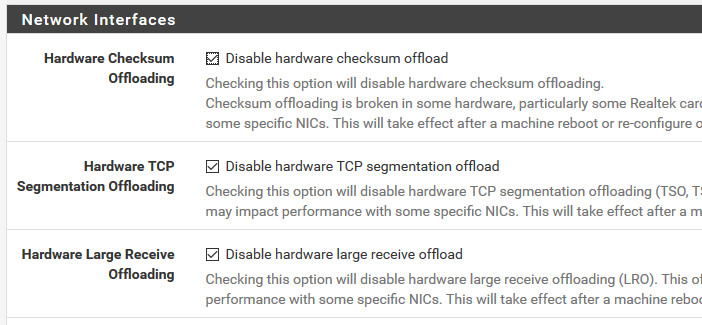
My PfSensen, dedicated to VPN, is virtualized. The only things you need to make sure, are :
- use VirtIO as interface
- disable hardware offload.

Vincent C.
Read more posts by this author.